The cybersecurity influencer market operates differently from B2C. The audience is small, technically literate, and quick to dismiss content that reads like vendor marketing dressed up as commentary. Practitioners follow other practitioners, not brand accounts, and the dominant channel is LinkedIn rather than YouTube or Instagram.
Finding the right people requires a different starting point than a standard influencer search. Follower count matters less than whether the audience engages, and engagement means replies from named peers, not emoji reactions. Below are the signals worth looking for and the two platforms that have become well-known reference points in the cybersecurity vendor community for this kind of discovery.
"In cybersecurity, 10,000 followers from practitioners will outperform 100,000 followers from a general tech audience on nearly every metric that matters."
At a glance
| Platform | Type | Entry | Best for |
|---|---|---|---|
| Favikon | Discovery & analytics | Free tier | Finding and vetting creators |
| Cyfluencer | Content distribution marketplace | Pay per post | Distributing content through creators |
What to look for before outreach
Before using any platform, it helps to know what you are looking for. Three signals are worth prioritising.
Engagement quality over follower count. A creator with 12,000 followers and consistent comment threads from CTOs, architects, and practitioners is more valuable to most vendors than one with 80,000 followers and minimal replies. Look at who is commenting, not just how many people are.
Niche specificity. A creator who posts across cloud infrastructure, developer tooling, application security, and mobile threat research in the same month is harder to align to a specific vendor message than one who stays in a single vertical. Check twelve months of posting history, not just recent content.
Practitioner voice vs promoter voice. The most effective cybersecurity influencers read as peers sharing opinions. If the tone of their sponsored posts shifts noticeably compared to their organic content, their audience will notice too. The best placements are ones where the creator genuinely uses or engages with the category the vendor sits in.
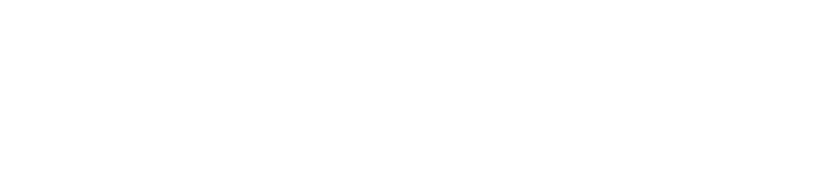
01Favikon
favikon.com
Favikon is a creator analytics platform with public ranking pages for specific verticals. The cybersecurity creator ranking lists LinkedIn creators sorted by follower count and engagement, filtered to the IT and cybersecurity category. This is a useful starting point before subscribing to any paid tier: you can browse who is active in the space, check their platform presence, and build an initial shortlist at no cost.
The paid platform adds engagement rate data, audience demographic breakdowns, and content performance metrics over time. For a vendor team building a shortlist from scratch, these metrics give enough signal to separate genuine community voices from accounts with large follower counts built on content that stopped performing years ago. The free tier is worth checking first, particularly the cybersecurity creator rankings, before committing to a subscription.
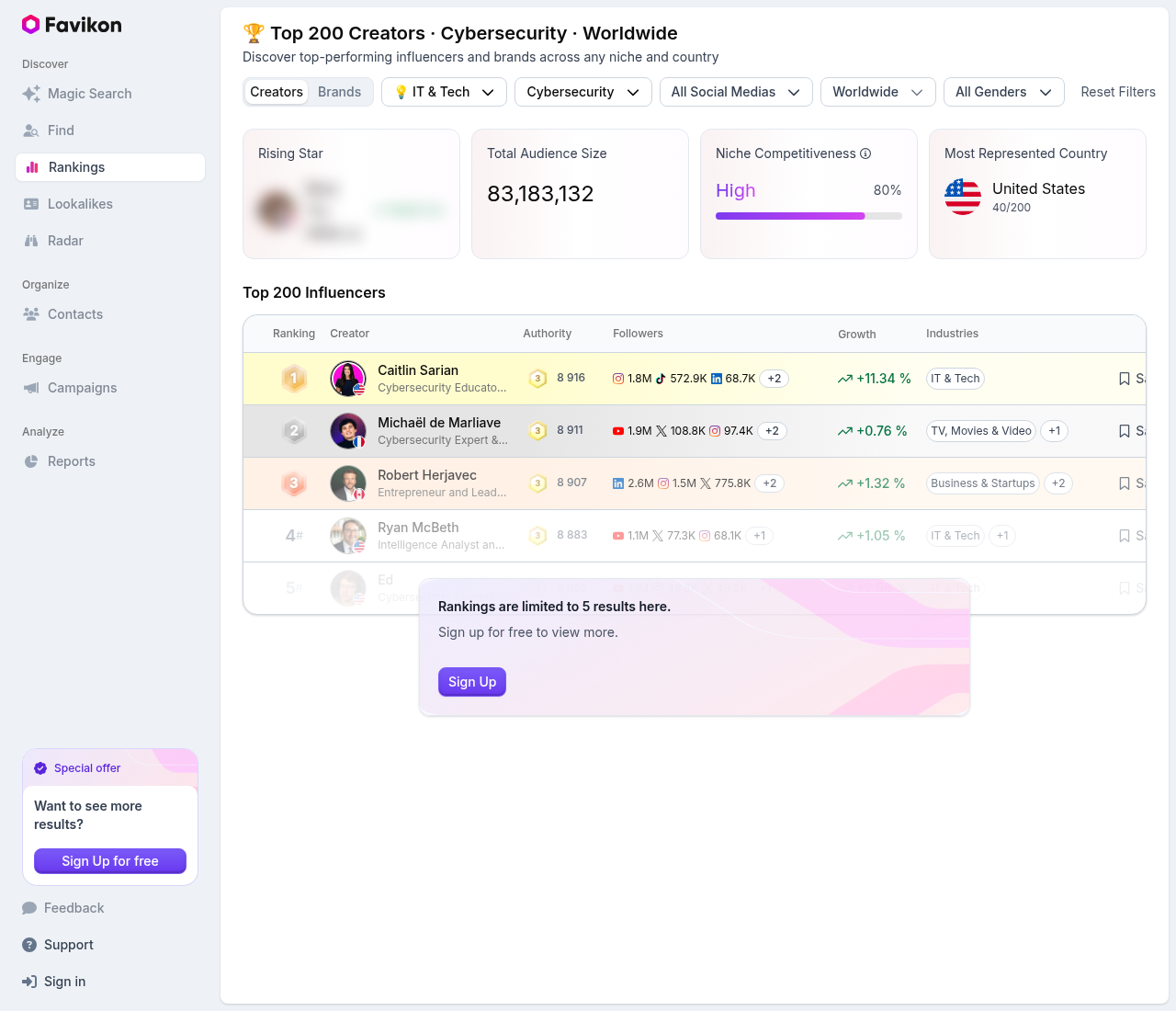
02Cyfluencer
cyfluencer.com
Cyfluencer is built specifically for the cybersecurity market. Vendors upload content to a shared library, including articles, whitepapers, and webinars, set a base fee per post and a pay-per-click rate, and creators in the network share that content with their audiences. The model is closer to sponsored distribution than traditional influencer marketing: you are paying for a placement, not building a relationship with a single creator.
The library includes active content from vendors across the security market. For a vendor that has existing content but no established distribution network, Cyfluencer provides an immediate audience without requiring one-to-one outreach to individual creators. The trade-off is that placement quality varies across creators in the network, and there is less control over which creator shares which piece compared to a direct relationship.
Organic discovery without a platform
Platforms accelerate the process but are not required. A manual search on LinkedIn using terms like "cybersecurity consultant," "CISO," "threat researcher," or category-specific terms like "identity security," "endpoint protection," or "cloud security" will surface active creators. Filter by "People" and sort by connection degree to prioritise creators with existing ties to your network.
The selection process is slower, but direct outreach to a creator you have already engaged with organically (liked posts, left substantive comments, shared their research) lands with a materially higher response rate than a cold message sent via a platform. For vendors with a narrow target vertical and a defined creator profile, the manual route often produces better placements.
Influencer amplification works best alongside an existing content programme. Without consistent owned content for the influencer to anchor to, even high-reach posts struggle to convert visits into subsequent engagement.