01Summary
TryHackMe was launching SEC1, a new entry-level hands-on cybersecurity cert, into a brutal cyber job market where "entry-level" listings routinely ask for five years of experience. They needed sponsored creative that would land with the actual audience: career changers, aspiring practitioners, and bug hunters trying to build provable skills without the boot-camp treadmill.
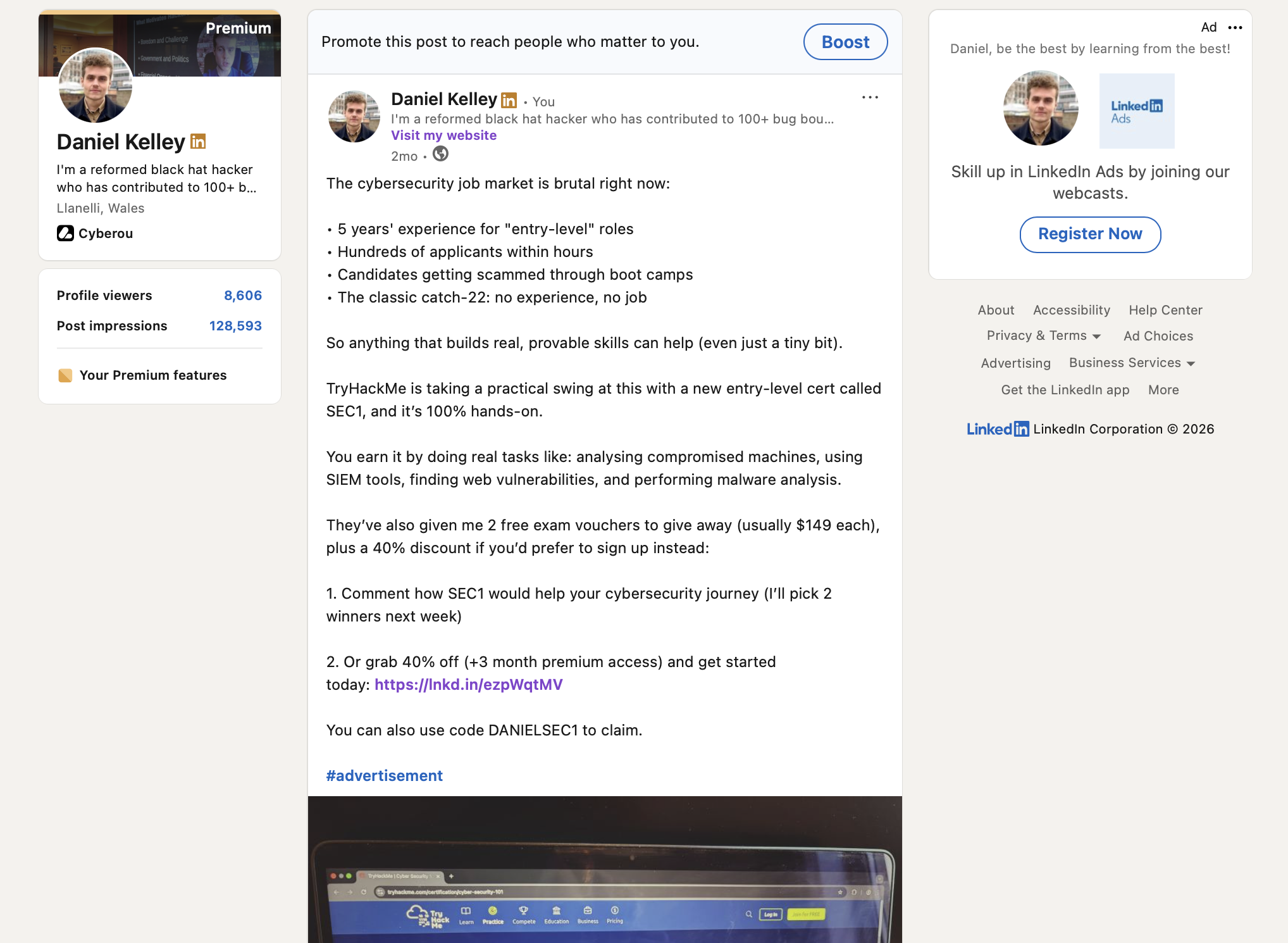
We ran a sponsored series from a practitioner account, anchored to the job market angle and the SEC1 launch. The standout post cleared 156K views, 548 likes, and 601 link clicks, with 2 free exam vouchers (worth $149 each) and a 40% discount code driving the engagement mechanic. Shivam Singh, TryHackMe's Growth Marketing Manager, left a public testimonial.
02Challenge
The cybersecurity job market is genuinely brutal. Entry-level listings ask for five years of experience; hundreds of applicants hit every junior role within hours; certified candidates still get rejected for not having a piece of paper nobody can agree on. Aspiring practitioners are skeptical of training platforms specifically because the market has taught them that no single cert changes the catch-22.
TryHackMe was launching SEC1 into that skepticism. The cert had to be framed as practical (hands-on tasks, not multiple-choice rote) and the sponsored creative had to lead with the problem the audience lives with, not with the product that allegedly solves it. A post that opened with "we're excited to announce SEC1" would have been scrolled past by the exact audience the launch needed to reach.
Engagement mechanics had to stay legitimate. Free exam vouchers and discount codes are the obvious hooks, but they also attract freebie-chasers who never convert. The mechanics had to pull in practitioners who would actually do the cert, not people hunting for a random giveaway.
03Approach
We opened the standout post with the cybersecurity job market reality: five years of experience for entry-level roles, applicants buried within hours, candidates getting burned by shady boot camps. That frame is something the audience lives with, not a marketing claim they can dismiss.
Then we named SEC1 and what it actually does. 100% hands-on, real tasks like analysing compromised machines, using SIEM tools, finding web vulnerabilities, performing malware analysis. The reader gets why this cert is different from the multiple-choice exams everyone already has an opinion on.
The hook stacked two mechanics: 2 free exam vouchers ($149 each) as a comment-to-win, plus a 40% discount code for readers who just wanted to sign up. Both mechanics used the DANIELSEC1 tracking code so TryHackMe could see real conversions, not just reach. Sponsored disclosure ran at the bottom of the body.
04Results
The standout post cleared 156K views, 548 likes, and 601 link clicks on LinkedIn. For a sponsored training-platform post in a saturated category, 601 link clicks is the signal that matters more than the impression count: that is real conversion intent, not just scroll-past reach.
The comment section stayed on topic. People engaged with the cybersecurity job market reality and what SEC1 would do for their journey, which is exactly the conversation TryHackMe wanted around a new cert launch. Freebie-chasers were rare because the mechanic required a real comment about the cybersecurity journey, not a low-effort keyword.
For TryHackMe, the series gave growth a reusable template for launching future certs: peer-framed, problem-led, single-CTA, specific hooks.

"Daniel was great to work with on our LinkedIn campaign for TryHackMe. He was very prompt, communication was easy throughout, and we'd absolutely love to collaborate with him again."
See more programmes in the case study library. For a brief tailored to your category, the contact page has the form.